Cybersecurity Services
Cyberattacks are no longer a problem reserved for large corporations. Today, small and mid-sized businesses are among the most frequently targeted, precisely because attackers know they often lack the defenses that enterprise organizations have in place. A single successful breach can result in stolen data, crippled operations, regulatory fines, and lasting damage to your reputation.
The question is no longer whether your business will be targeted. The question is whether you’ll be ready when it happens.
At Total Business Systems, we provide comprehensive cybersecurity services designed to protect your people, your data, and your operations from the full spectrum of modern cyber threats. We combine advanced security technology with expert human oversight to build layered defenses that stop attacks before they cause damage and respond rapidly when threats emerge.
How Can We Help?

Why Cybersecurity Can No Longer Be an Afterthought
The cybersecurity landscape has changed dramatically. Threats that once required sophisticated nation-state resources are now available to any criminal with a laptop and an internet connection. Ransomware, phishing, business email compromise, and supply chain attacks are hitting businesses of every size and industry, and the consequences are severe.
According to industry research, the average cost of a data breach for a small to mid-sized business now runs into the hundreds of thousands of dollars when you factor in downtime, recovery costs, legal fees, regulatory penalties, and lost customers. Many businesses never fully recover.
At the same time, regulatory requirements around data protection are tightening. Businesses in healthcare, finance, legal, and other sectors face serious legal exposure if they fail to implement and demonstrate adequate cybersecurity controls.
The good news is that the right cybersecurity partner makes robust protection achievable and affordable for any organization, regardless of size.
Our Cybersecurity Services
Total Business Systems delivers comprehensive cybersecurity services designed to protect your business from evolving threats, minimize risk, and ensure operational continuity. Our layered approach combines advanced security technologies with expert oversight to keep your systems secure, compliant, and resilient.
24/7 Threat Detection and Response
Cyber threats do not follow a schedule, and neither do we. Our Security Operations Center provides continuous monitoring of your environment, using advanced threat intelligence and behavioral analytics to detect suspicious activity in real time. When a threat is identified, our security engineers act immediately to contain, neutralize, and remediate the issue before it escalates.
Email Security and Anti Phishing Protection
Phishing attacks remain one of the most common causes of security breaches. Our email security solutions block malicious messages before they reach your team, with advanced detection for spoofing, impersonation, and harmful attachments or links. We also implement DMARC, DKIM, and SPF protocols to safeguard your domain and prevent abuse.
Endpoint Detection and Response (EDR)
Every device connected to your network can become a potential entry point for attackers. Our EDR solutions go beyond traditional antivirus by using machine learning and behavioral analysis to detect and stop advanced threats, including zero day exploits and fileless malware, across all endpoints such as workstations, laptops, and mobile devices.
Firewall Management and Network Security
A poorly configured firewall can leave your business exposed. We manage and optimize your firewall and network security infrastructure to ensure only authorized traffic flows in and out of your environment. This includes intrusion detection and prevention systems, network segmentation, and secure remote access configuration.
Identity and Access Management
Compromised credentials are a leading cause of data breaches. We implement multi factor authentication, single sign on, privileged access controls, and least privilege policies to ensure only authorized users can access critical systems. This reduces the risk of unauthorized access even if login credentials are exposed.
Security Awareness Training
Your employees play a critical role in your cybersecurity posture. Our training programs educate your team on recognizing phishing attempts, social engineering tactics, and other common threats. Ongoing simulated phishing campaigns help reinforce best practices and improve security awareness over time.
Vulnerability Assessments and Penetration Testing
Identifying weaknesses is the first step to strengthening your defenses. We conduct comprehensive vulnerability assessments to uncover risks across your infrastructure, applications, and configurations. Our penetration testing services simulate real world attacks to identify exploitable vulnerabilities before cybercriminals can take advantage of them.
Cybersecurity Compliance and Risk Management
Achieving compliance requires more than checking boxes. We help your business align with industry standards such as HIPAA, PCI DSS, SOC 2, CMMC, and NIST. Our team conducts gap analyses, develops remediation strategies, and maintains the documentation needed to demonstrate compliance to auditors and stakeholders.
Data Loss Prevention and Encryption
Protecting sensitive data is essential for business continuity and compliance. We implement data loss prevention strategies and encryption solutions to secure your information both at rest and in transit. This ensures your data remains protected even if devices are lost, stolen, or compromised.
Incident Response Planning
No system is completely immune to cyber threats. What matters is how prepared you are to respond. We help you build a clear and actionable incident response plan so your team knows exactly how to respond, who to contact, and how to minimize impact in the event of a security incident.
Our Clients Stay With Us Because We Show Up
Service, consistency, and care are what set us apart.

Flexible Support That Goes the Extra Mile
“We had TBS come out to run cable down to our home office and set up a separate network extender. We had issues with our network extender but they were willing to work with us to get it resolved without running out all our support hours. I appreciate their flexibility and look forward to utilizing them for support down the road.”
Rachel Cardy
Jacksonville, FL
The Total Business Systems Cybersecurity Approach
We believe cybersecurity should be layered, proactive, and built around your specific risk profile — not a generic checklist applied the same way to every business.
Our approach follows a proven framework built on five core principles:
- Identify — We start by understanding your environment, your assets, your data flows, and your risk exposure. You can’t protect what you haven’t mapped.
- Protect — We implement the technical and administrative controls necessary to reduce your attack surface and defend against known threat vectors. This includes everything from firewall rules and patch management to access policies and employee training.
- Detect — We deploy monitoring tools and human oversight to identify threats that bypass preventive controls as quickly as possible. The faster a threat is detected, the less damage it can cause.
- Respond — When an incident occurs, speed and decisiveness matter. Our security engineers execute a structured response to contain the threat, preserve evidence, and restore normal operations with minimal disruption.
- Recover — We help you return to full operational capacity after an incident, conduct a thorough post-incident analysis, and implement lessons learned to strengthen your defenses going forward.
Choose Total Business Systems for Cybersecurity
1
Deep Technical Expertise
Our security team holds industry recognized certifications including CISSP, CEH, CompTIA Security+, and Microsoft Security credentials. We bring real world expertise to every engagement, not generic, one size fits all solutions.
2
Vendor Agnostic Recommendations
We are not tied to any single security vendor. Instead, we evaluate your environment and recommend the most effective tools based on your needs, budget, and risk profile, always prioritizing your protection over partnerships.
3
Business First Security Approach
We design security programs that support productivity, not hinder it. Overly restrictive controls often lead to employee workarounds that create new risks, so we focus on balanced security that protects your business while keeping operations efficient.
4
Transparent Security Reporting
You always have clear visibility into your security posture. We provide regular reporting, risk summaries, and easy to understand insights so leadership teams can make informed decisions without technical complexity.
5
Scalable Security Solutions
Whether you are a five person professional firm or a 300 employee organization with complex infrastructure, our cybersecurity services scale with your business size, industry requirements, and growth plans.
6
Proactive Threat Intelligence
We continuously monitor emerging threats, vulnerabilities, and attacker tactics to keep your defenses up to date. This proactive approach ensures your security evolves alongside the threat landscape.
Industries We Serve
Cybersecurity requirements vary significantly by industry, and a one-size-fits-all approach simply doesn’t work. Total Business Systems has experience delivering cybersecurity programs tailored to the specific risks, workflows, and compliance obligations of businesses across a broad range of sectors, including:
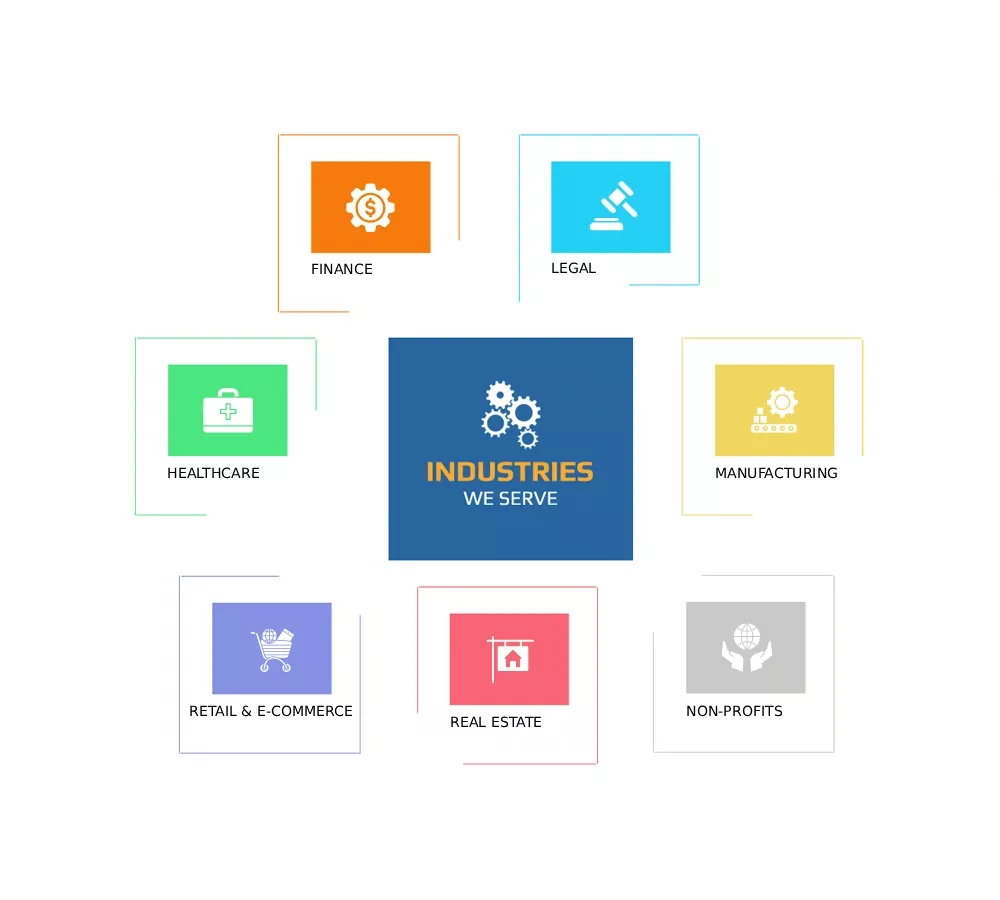
- Healthcare and medical practices navigating HIPAA requirements
- Financial services firms managing sensitive client and transaction data
- Legal and professional services organizations protecting privileged information
- Manufacturing and industrial businesses securing operational technology environments
- Non-profits and educational organizations with limited budgets and high exposure
- Real estate firms managing large volumes of financial transactions and personal data
- Retail and e-commerce businesses protecting payment card data under PCI-DSS
Regardless of your industry, our security programs are built around your specific threat environment, not generic best practices designed for someone else’s business.
What Happens If You Don't Act?
The risks of inadequate cybersecurity are not theoretical. Businesses without proper defenses face real, near term exposure.
Ransomware attacks can lock your entire organization out of critical systems for days or even weeks, with attackers demanding payments that often reach tens of thousands of dollars, with no guarantee of recovery even if the ransom is paid. Phishing attacks can lead to fraudulent wire transfers, stolen customer data, and compromised vendor relationships. A single unpatched vulnerability can give attackers silent, long term access to your network without detection.
Beyond the immediate financial impact, a cybersecurity incident can create lasting consequences, including regulatory investigations, legal liability, loss of customer trust, and reputational damage that can take years to recover from.
The cost of prevention is significantly lower than the cost of recovery. The right time to strengthen your defenses is before an incident occurs, not after.

Frequently Asked Questions
All businesses with email, internet access, or customer data are at risk. Risk increases with outdated systems, no multi-factor authentication, weak employee training, or lack of backups and monitoring. A cybersecurity assessment from Total Business Systems helps identify your exact risks and improvement steps.
Managed IT services cover overall IT support like help desk, network management, and cloud systems. Cybersecurity focuses specifically on protecting your business from threats like hacking, ransomware, and data breaches. It includes threat detection, security monitoring, and incident response.
Yes. Small and mid-sized businesses are frequent targets because they often have weaker security. Many attacks are automated and scan all businesses for vulnerabilities. Small companies are also targeted as entry points into larger partner organizations.
Basic cybersecurity protections such as endpoint security, email protection, and multi-factor authentication can typically be deployed within 2 to 4 weeks. More advanced solutions like compliance or full security monitoring may take longer depending on your environment.
Immediately isolate affected systems, avoid shutting them down, and contact your IT or cybersecurity provider. Quick containment is critical to prevent further damage. A formal incident response plan helps reduce downtime, data loss, and recovery costs.
Your Business Is Worth Protecting. Let's Make Sure It Is.
Cybersecurity threats are not slowing down and neither are we. Total Business Systems is ready to assess your current security posture, identify your most critical vulnerabilities, and build a protection strategy designed around your business.
Contact us today to schedule your free cybersecurity assessment. No pressure, no jargon, just a clear picture of where you stand and what it takes to stay protected.