Leading-edge voice and data wiring solutions
Voice and data cabling is a type of structured cabling that allows for communication within and between businesses. It involves installing different types of cables, such as coaxial and fiber-optic, to connect devices like phones, computers, TVs, and copiers. Voice and data cabling requires professional installation technicians who have the right tools and skills to handle the infrastructure wiring of commercial buildings. Voice and data cabling also offers benefits such as high speed, reliability, scalability, and easy upgrades.
Upgrade Your Infrastructure Wiring
Having the latest coax and fiber-optics infrastructure can have many benefits for consumers, businesses and society.

Faster Speeds
Faster and more reliable internet speeds. Fiber-optic networks can provide symmetrical upload and download speeds that are much higher than copper networks, which were originally built for voice services and degrade over long distances. Coaxial networks can also offer faster speeds than copper, but they are still limited by the length and quality of the copper wire.
Future Proofing
Future-proof technology. Fiber-optic networks have almost limitless potential, as they use pulses of light to transmit information and are not constrained by the capacity of the line. As internet demand and technology evolve, fiber networks can easily adapt and meet the new requirements without needing to upgrade the infrastructure.
Low Latency
Lower latency and better quality. Fiber-optic networks have lower latency, which means less delay and lag in data transmission. This can improve the quality of online activities such as video conferencing, gaming, streaming and cloud computing. Coaxial networks also have lower latency than copper, but they are more susceptible to signal interference and loss.
Cost Savings
Cost savings and environmental benefits. Fiber-optic networks can reduce operational and maintenance costs for service providers, as they have longer life cycles and require less frequent repairs than copper networks. They can also save energy and reduce carbon emissions, as they use less electricity and generate less heat than copper networks.
Server & Network Cleanup Benefits
Keeping your IT server and network clean and organized can have many benefits for your business.
Uptime is everything when it comes to your company’s internet and phone service. We have the equipment and manpower to cover all of your wiring needs from computers, servers, data, networks, VoIP, video surveillance, access control, and point-of-sale systems. From designing your cable layout to installation, our professional technicians will manage your entire infrastructure to ensure fast and reliable voice and data transmission.
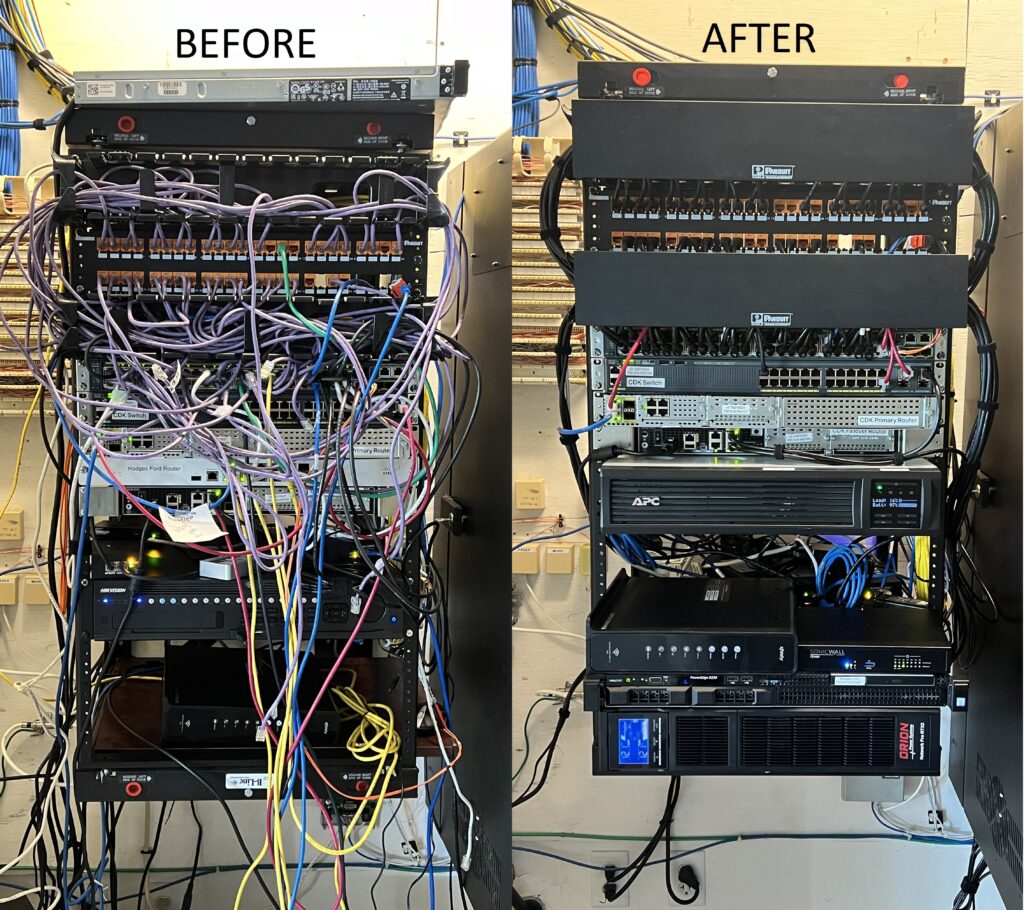
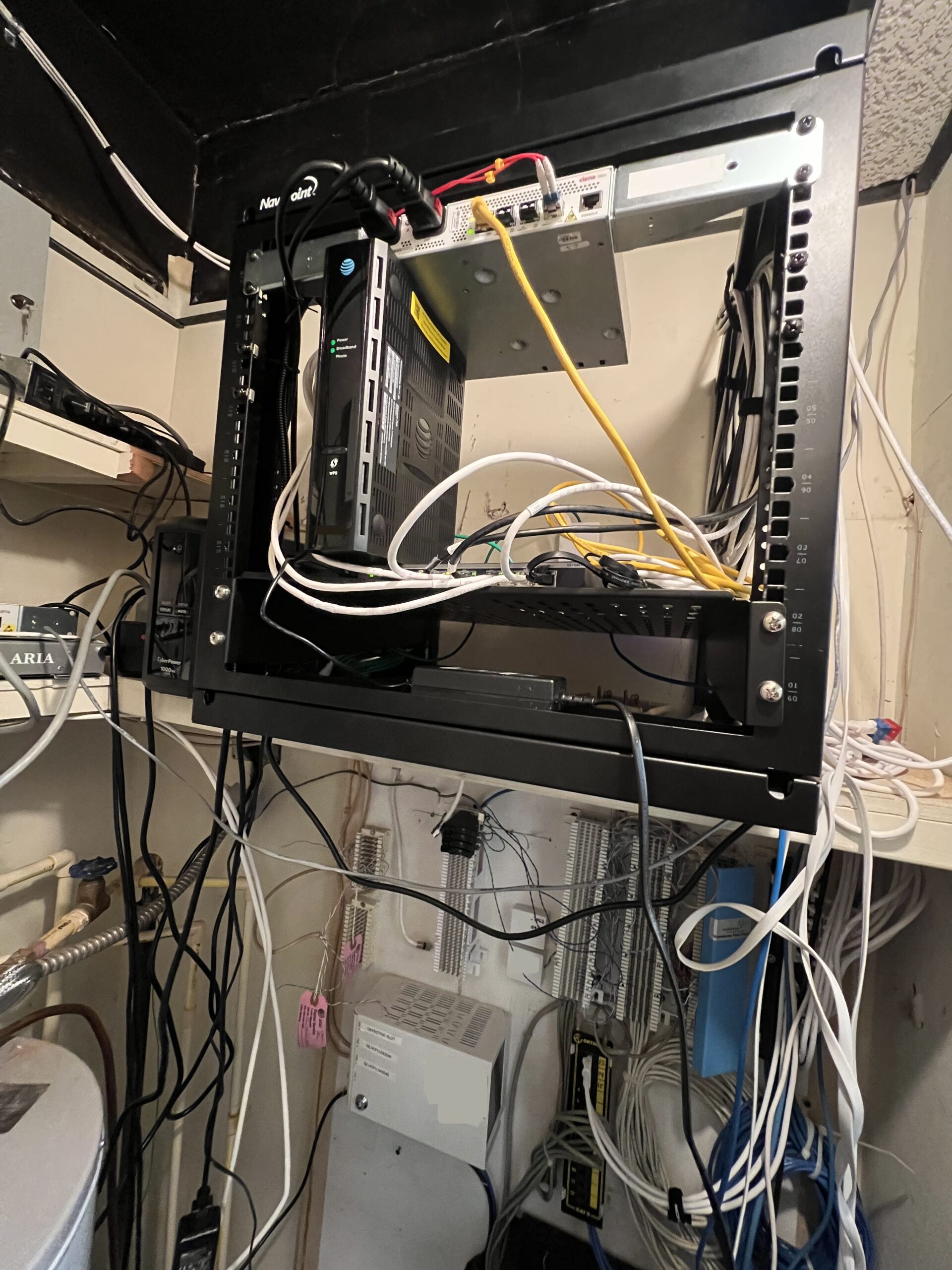
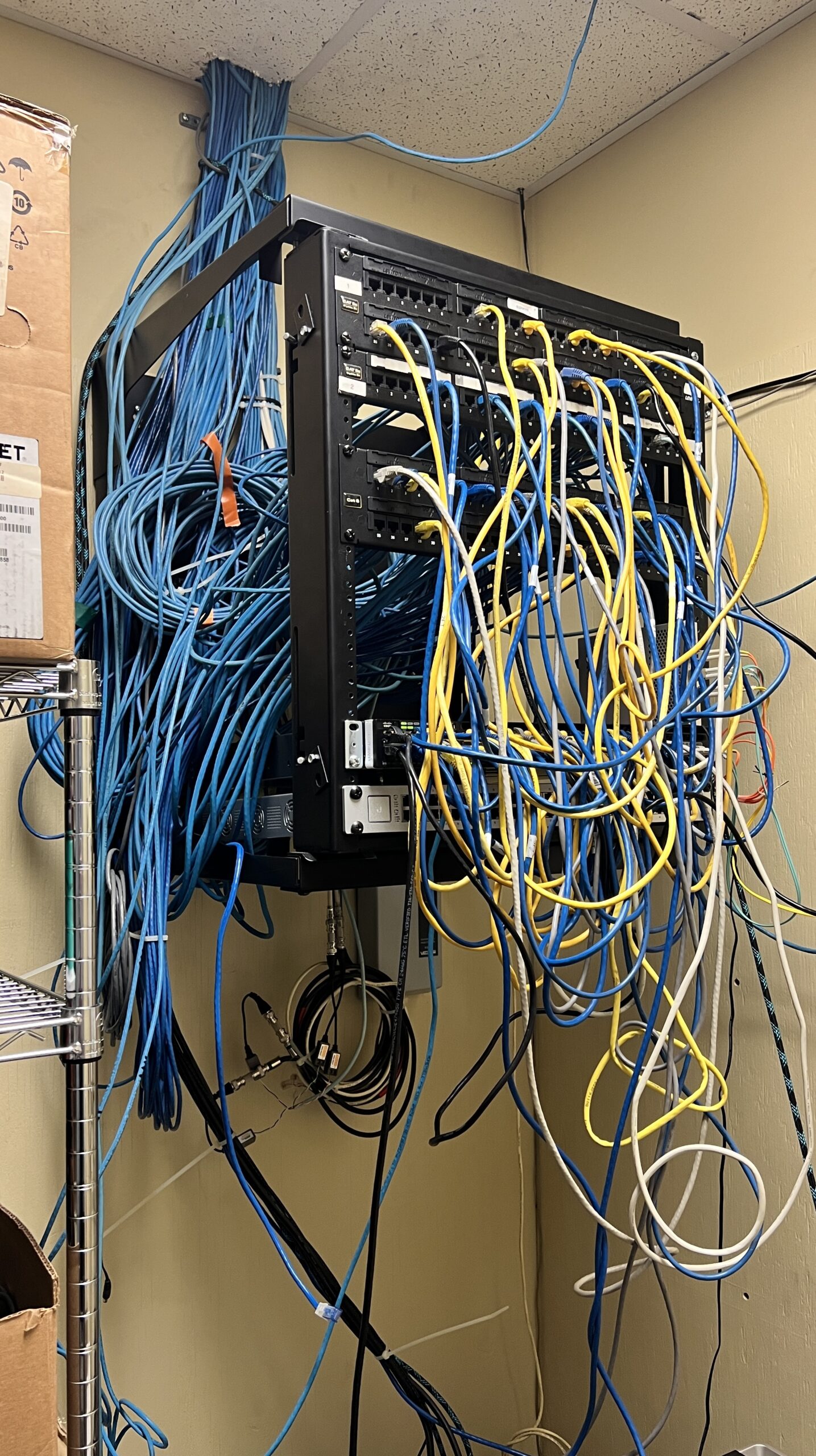
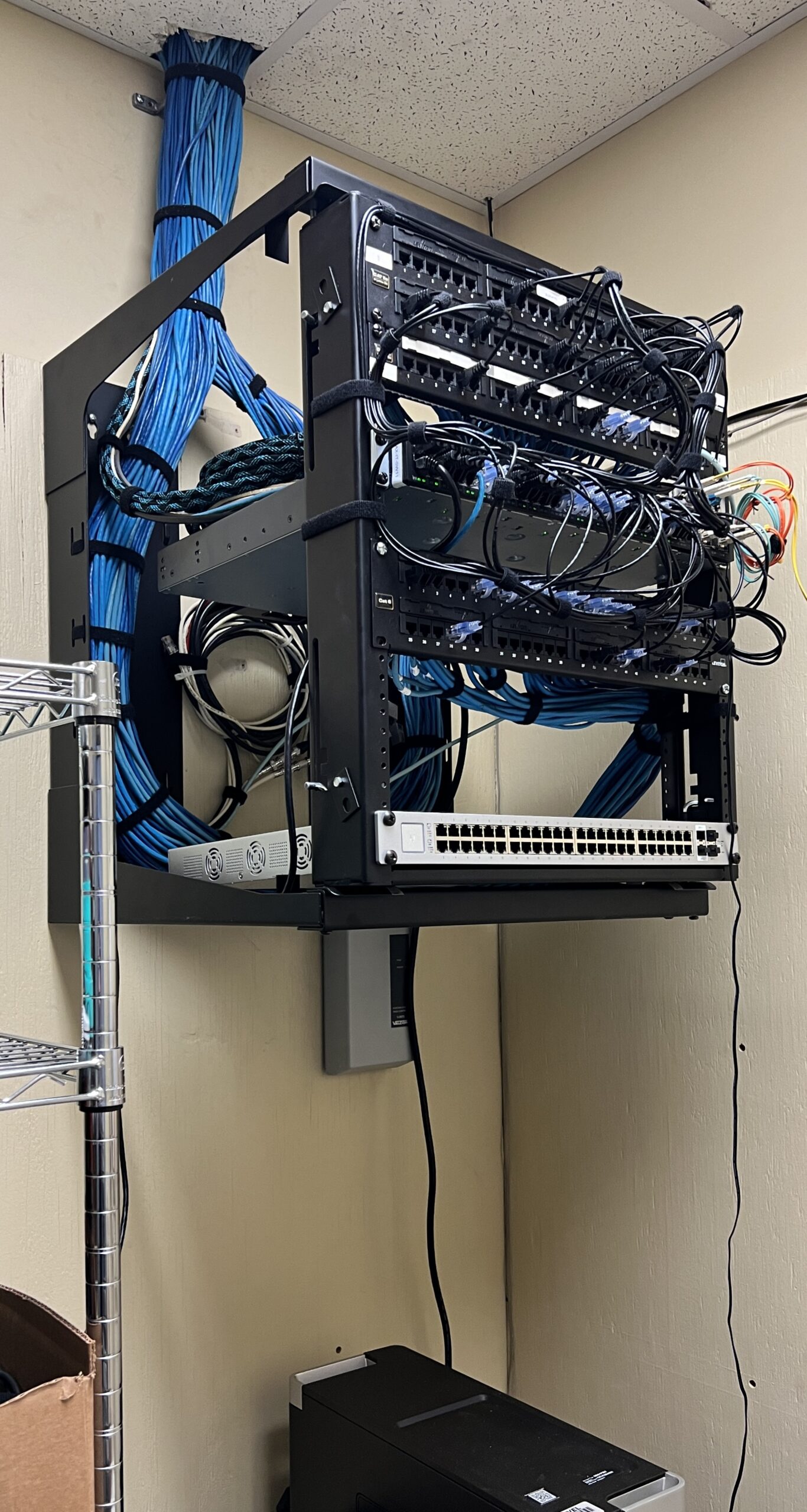
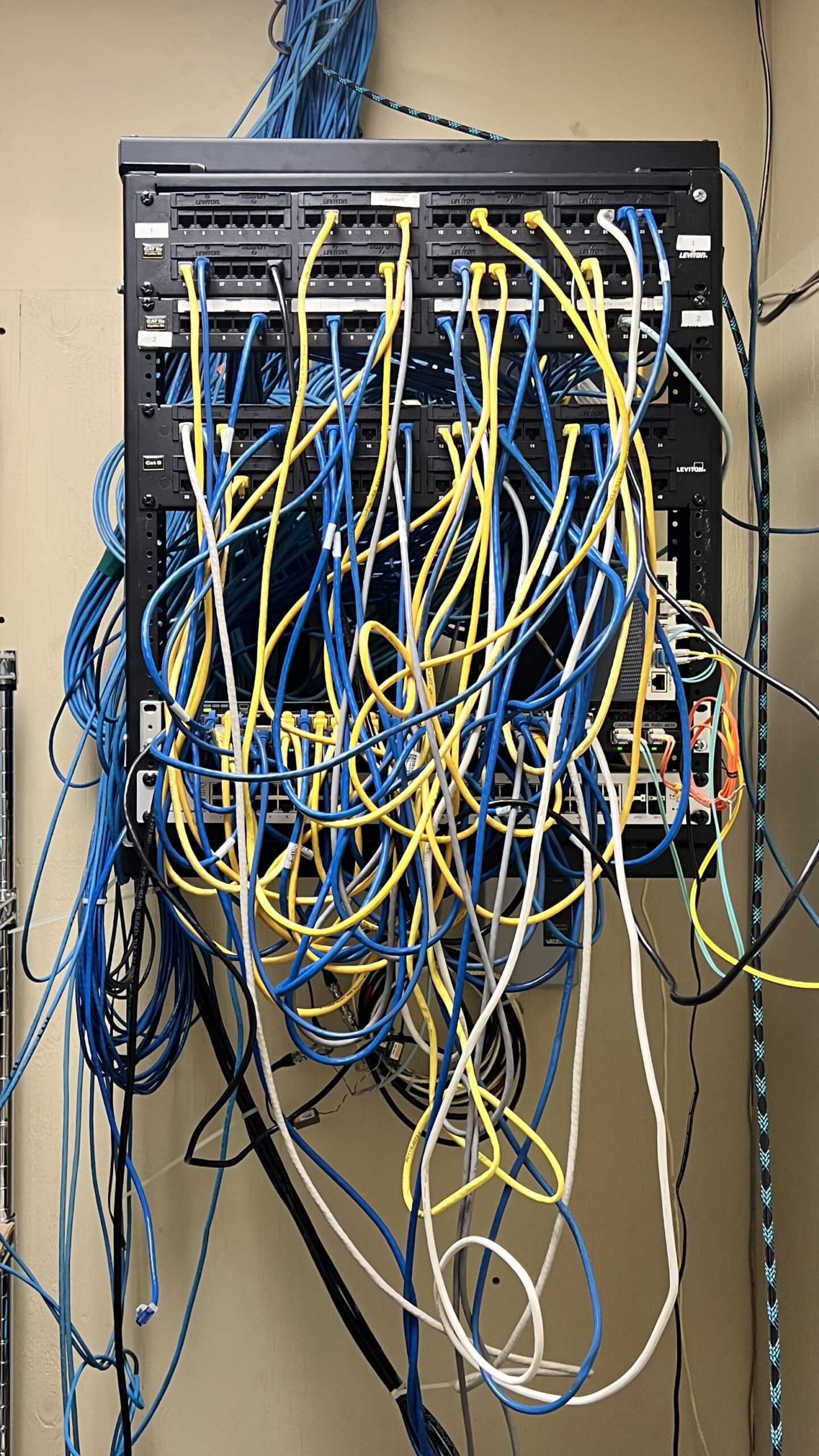
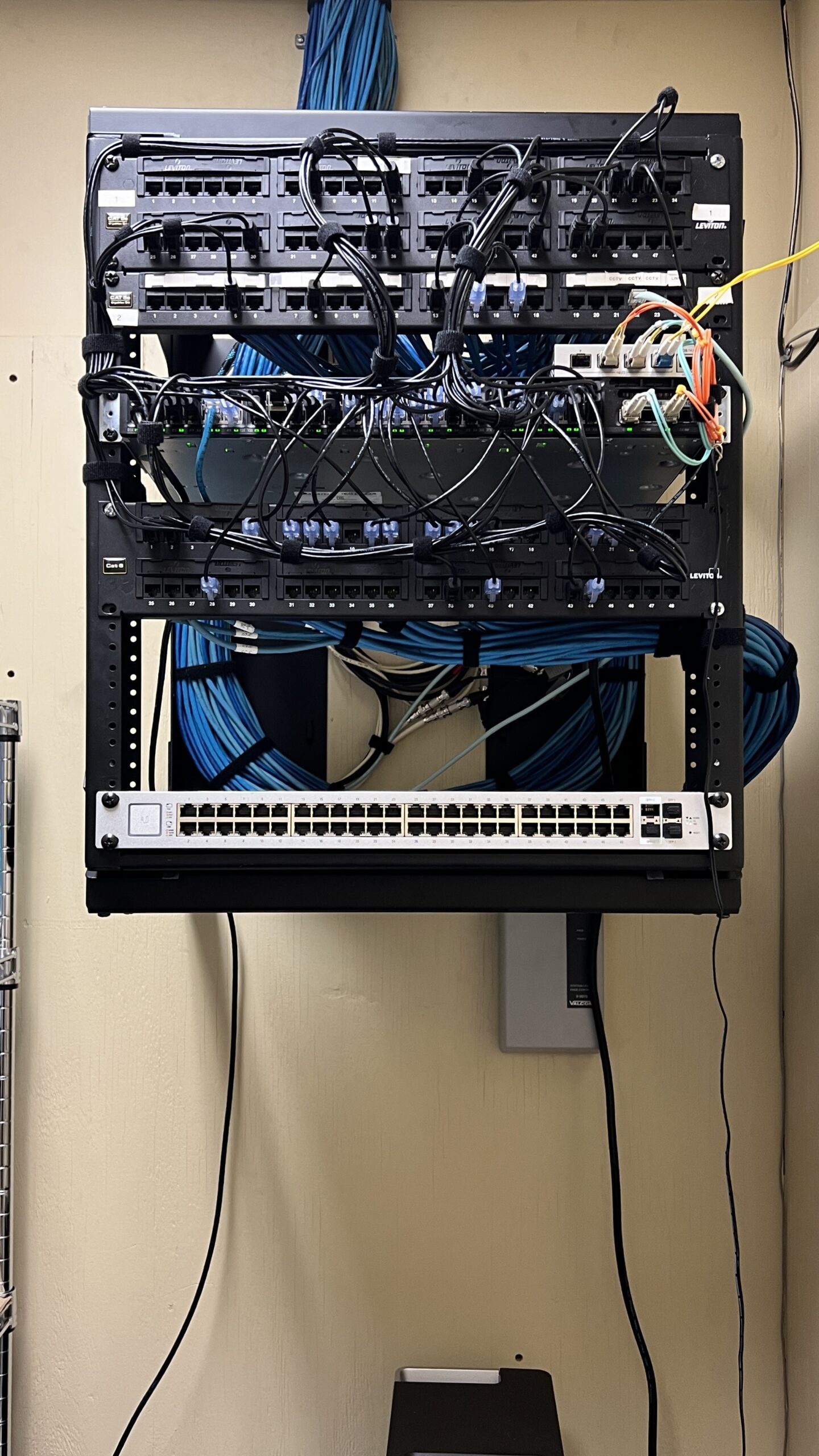
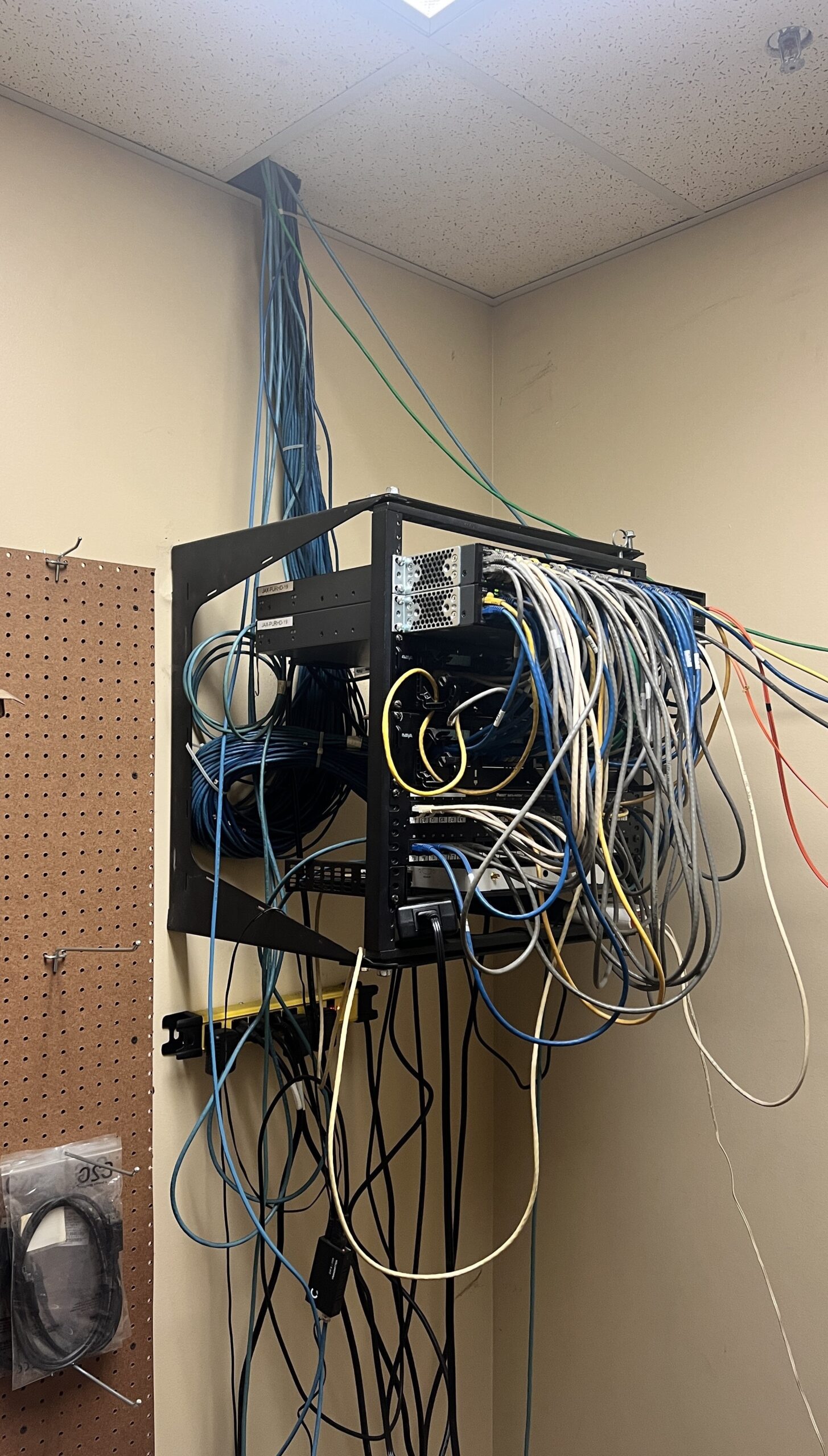
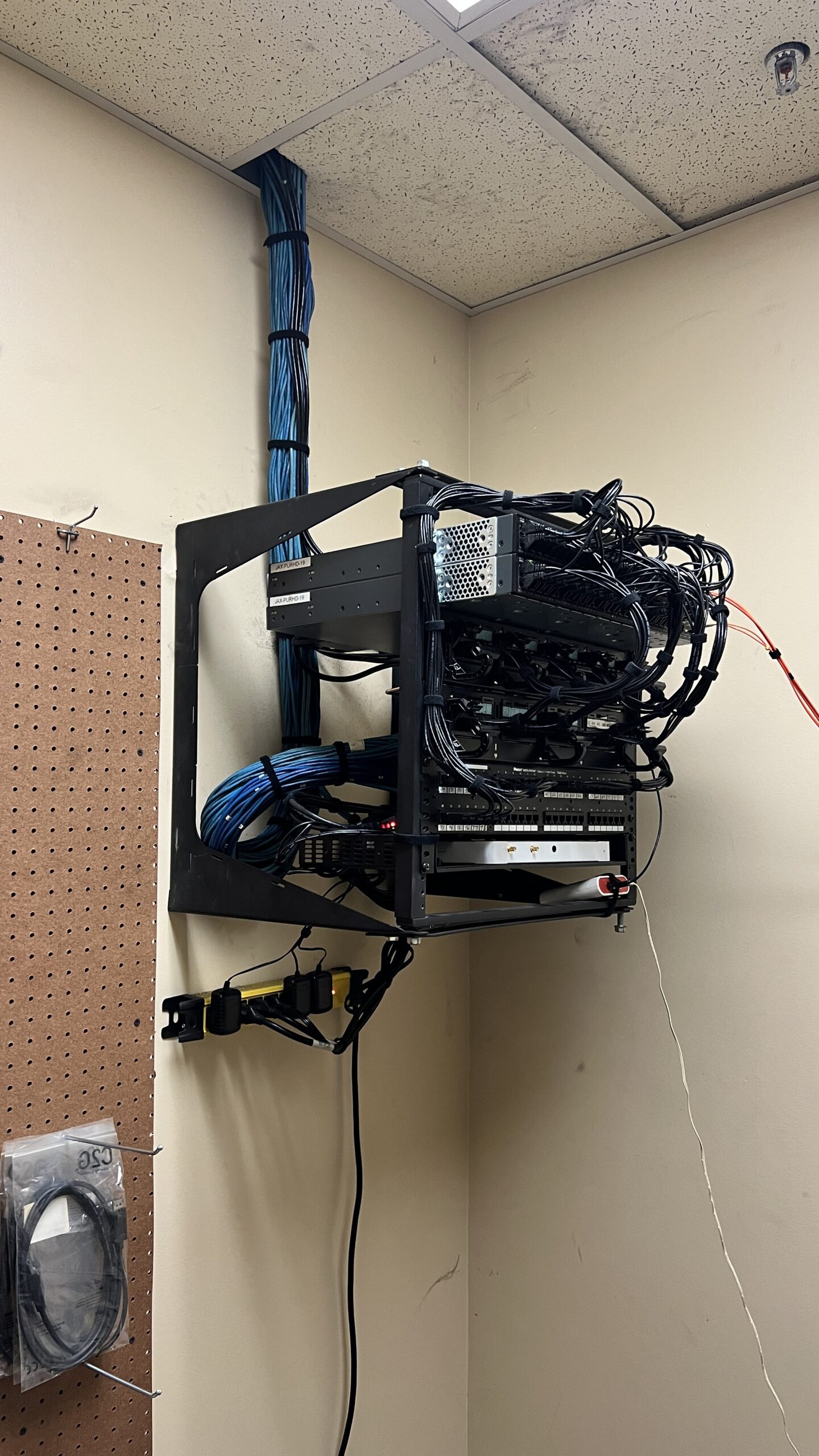
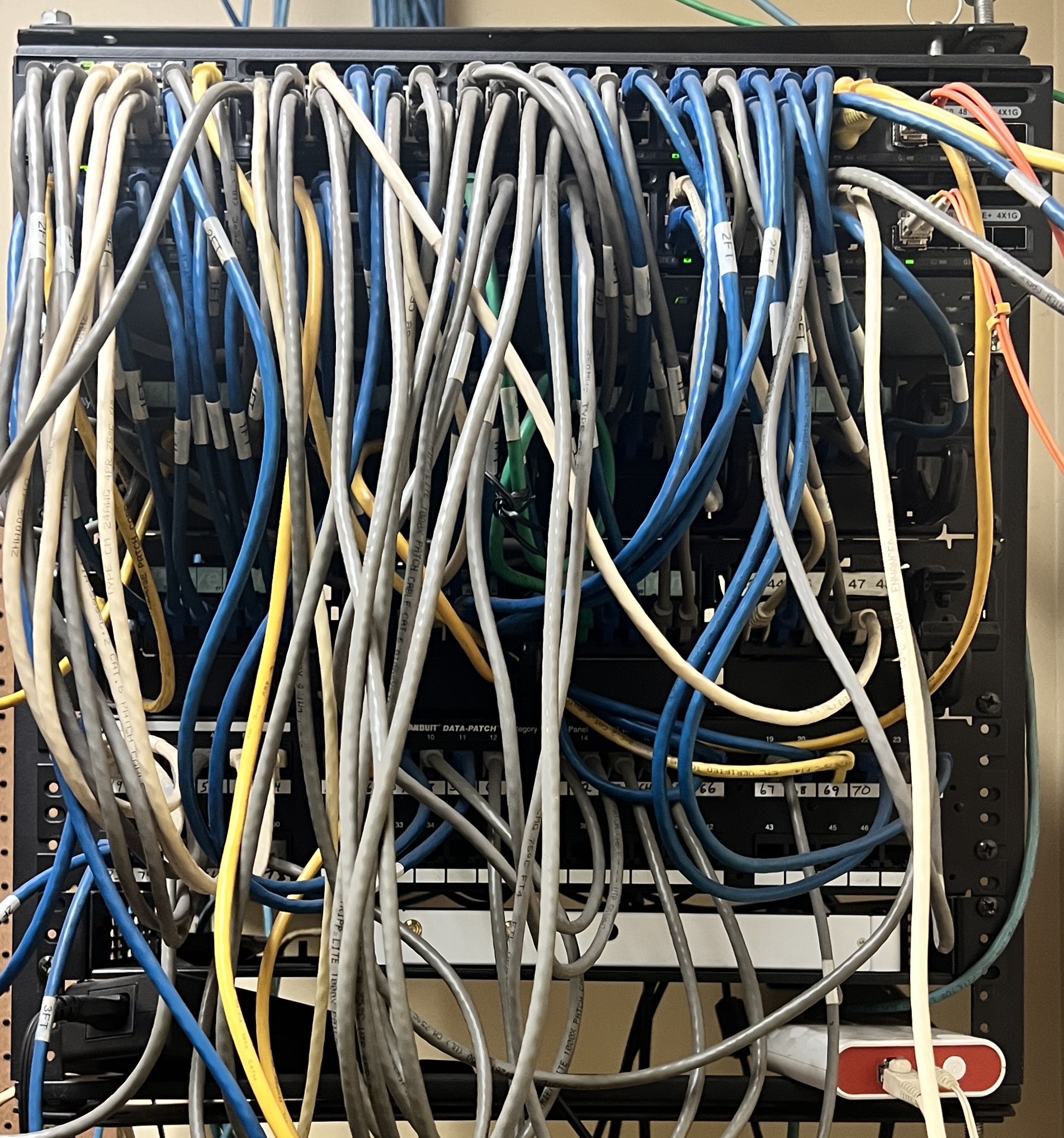
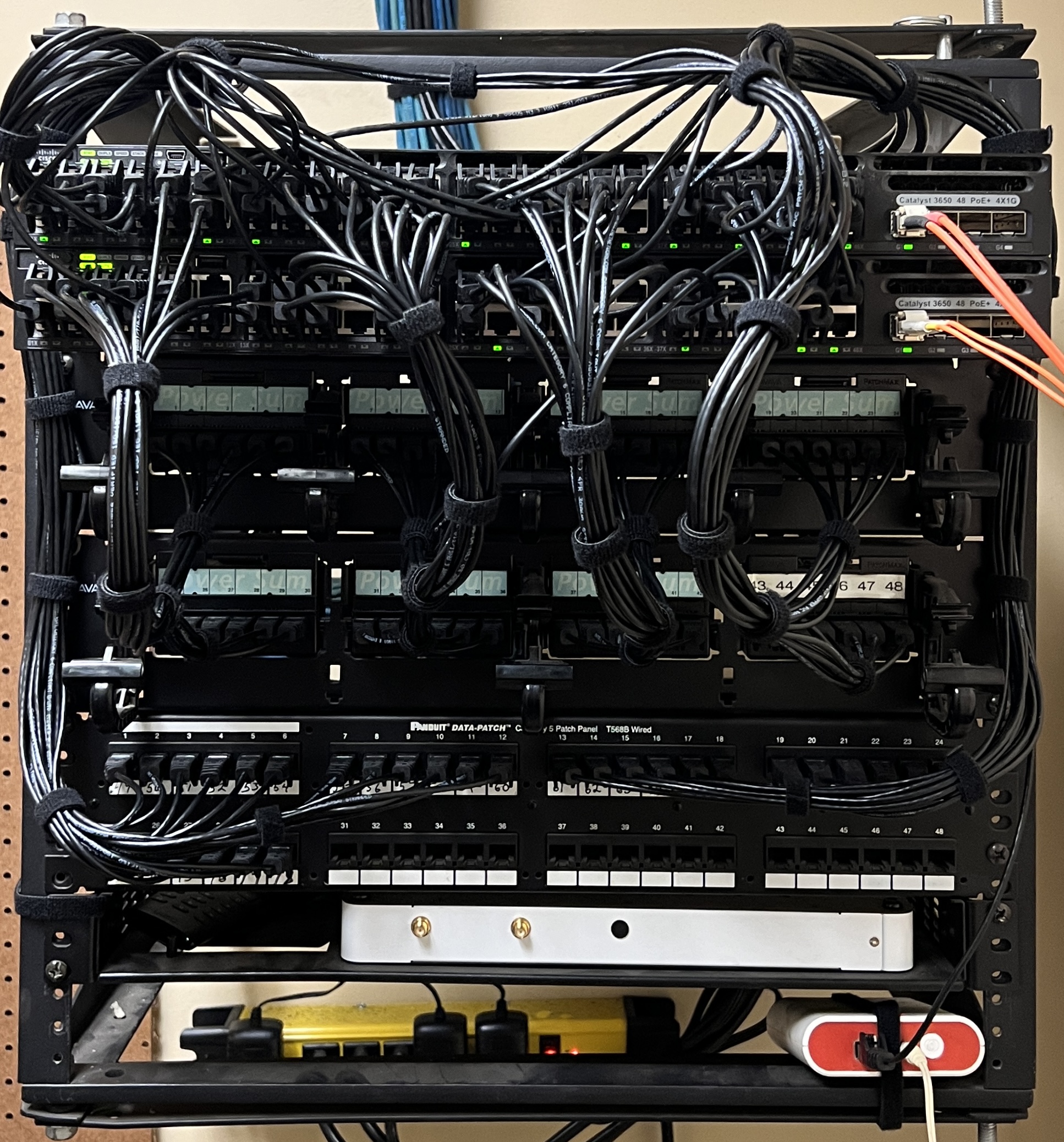
View some of our recent server cleanups here.
Test Your Internet Speed
Voice and Data Wiring services, benefits and features include:
Point-To-Point Wireless Connectivity
Server, network racks and enclosures
Fiber-Optic systems
Future proof your network and ensure proper cabling installation
Expand your office or building to connect more devices
Faster local network speeds to transfer data
Better shielding to help ensure data integrity and high-speed performance
Power your access points and desk phones with power over ethernet for years to come
Structure indoor, outdoor voice and data cabling
How Server Cleanup Reduces Network Troubleshooting Times by Up to 60%
In the realm of Information Technology (IT), maintaining the physical health of servers and network equipment is just as important as their digital upkeep.
Enhanced Performance
Regular physical cleanup of servers can prevent dust and debris buildup, which can cause overheating and hardware failure. By ensuring that servers are clean and well-maintained, hardware performance is optimized, leading to fewer network issues and reduced troubleshooting times.
Hardware Access
A clean and well-organized server room makes it easier for IT professionals to access hardware when needed. This can significantly reduce the time it takes to identify and resolve hardware-related network issues.
Cable Management
Proper cable management is an important part of physical server cleanup. By ensuring that cables are neatly organized and clearly labeled, IT professionals can more easily identify and resolve network issues related to faulty or disconnected cables.
Hardware Failures
Regular physical server cleanup can help prevent hardware failures. For example, removing dust can prevent overheating, which is a common cause of hardware failure. By preventing such failures, network troubleshooting times can be reduced.
Professional Server & Network Equipment Cleanup
Protect Your Server & Equipment With Proper Cabling And Routing